Network drift breaks segmentation. It happens when your network changes but your access controls fail to keep up. Organizations struggle with network access control because traditional solutions like 802.1X and RADIUS are too complex for modern, diverse networks. Network Lock takes a different approach: continuous visibility of what is on your network segments, combined with audit and block enforcement. No infrastructure overhaul. No agents. Just real control.
I’m sharing this because after 25 years in network and IT security—working on infrastructure operations, then vendor roles, and now co-founding IoT Secure—I’ve seen organizations trapped by the same false choice: accept partial control or spend months on infrastructure projects. That’s not how it has to be. Throughout my career with organizations from small businesses to Fortune 100 companies, I learned one thing: vendors are in the business of selling solutions. Organizations are in the business of solving the problems they actually have. And those two things don’t always align.
Today, I want to show you network access control done differently.
If you’re an IT leader, network architect, or security engineer responsible for network access control, this article is written for you. We’re going to talk specifically about network access control, or NAC—how to control what devices can access your network segments and what happens when that control breaks down. You’ll walk away understanding:
- Why traditional network access control deployments are expensive, complex, and often incomplete in real organizations
- What “network drift” actually is and why it matters for network access control
- How network drift connects to Zero Trust thinking, and why addressing it today positions you for stronger security tomorrow
- A practical approach to access control that doesn’t require massive infrastructure changes or months of implementation
Most importantly, you’ll understand that controlling your network doesn’t have to be an all or nothing, multiyear project. There’s a simpler path forward.
The Real Challenge: Cost and Complexity
When I talk to IT leaders about network access control, the conversation usually goes the same way. They mention 802.1X (the standard protocol for controlling what connects to a network), RADIUS servers, certificates, and projects that never quite crossed the finish line.
That pattern has been consistent for 20 years. Not because organizations are unprepared or lack commitment, but because traditional approaches to network access control assume conditions that don’t exist in most real organizations. They assume you can upgrade all your network infrastructure. They assume you have budget and staff for multiyear implementations. They assume your devices all support modern authentication.
The actual issue isn’t that network access control doesn’t work. It works in certain contexts—homogeneous corporate environments with managed endpoints, for example. The issue is that deploying comprehensive network access control across a modern, heterogeneous organization is genuinely expensive and complex. And in many cases, the return doesn’t justify the investment.
So organizations make rational decisions. They deploy access control where it makes sense. They accept limited deployments elsewhere. And then something unexpected happens: the network evolves. New devices appear. Requirements change. What they thought they had controlled begins to drift.
What You’re Actually Protecting (And How Drift Threatens It)
Before we talk about solutions, let me be direct about what we’re actually protecting when we talk about network access control. I’m not talking about compliance checkboxes or configuration standards. I’m talking about controlling what gets access to your most valuable assets and critical operations.
If you run a manufacturing facility, you’re protecting the systems that run production. Your plant floor network contains PLCs, sensors, and process control systems. These aren’t just computers. They’re the systems that keep your facility running, generating revenue, meeting commitments to customers. A production shutdown isn’t an inconvenience. It’s an existential threat to your business. Network access control for your plant floor means you know exactly what devices are on that network, and you can verify they’re supposed to be there. You can be confident that only authorized industrial systems are operating on those networks.
If you run a school, you’re protecting critical learning systems and student safety. Your IP camera segment contains cameras throughout hallways, classrooms, and facilities. These cameras are a crucial part of school security and operations. They monitor student areas during transitions. They protect staff in vulnerable situations. They provide evidence when incidents occur. They deter misconduct. Network access control for your camera segment means you know exactly what systems can access your camera feeds and the recordings. You can be confident that only authorized personnel have visibility into sensitive areas.
If you run a healthcare organization, you’re protecting patient systems and medical operations. Your clinical network contains patient monitoring devices, electronic health record systems, imaging systems, and clinical workflow tools. These systems directly impact patient care and safety. A compromised clinical system doesn’t just threaten privacy. It threatens lives. Network access control for your clinical network means you know exactly what devices are on that network and can verify they’re appropriate clinical systems with appropriate security postures.
In every case, unauthorized network access threatens something your organization has built and depends on. That’s why access control matters. That’s why knowing what’s on your network and controlling it is non-negotiable.
But here’s where it gets complicated. These networks evolve. Devices get added. Requirements change. The network you designed on day one looks different six months later. Sometimes those changes are expected and managed. Sometimes they’re not. Sometimes you know about them. Sometimes you discover them months or years later by accident. That uncontrolled, unknown change—the gap between what you designed and what you actually have—is network drift.
Why Network Drift Creates Real Risk
Now let’s understand what that drift actually means in each of these scenarios, because the consequences are specific and serious.
Manufacturing Facility: A company acquires new diagnostic equipment for the plant floor. A technician arrives with a portable device to troubleshoot process control systems. An engineer brings in temporary monitoring equipment to validate a new system. An IT person sets up a temporary connection for asset tracking. Each device gets connected temporarily. Each one is supposed to be removed. But nobody tracks them explicitly. Weeks later, they’re still connected. Months later, nobody remembers they’re there. Now your plant floor network contains devices you didn’t explicitly approve. Some have embedded software you’ve never audited. Some have default credentials that were never changed. Some are connected to the technician’s home office via VPN. If an unauthorized device connects to the plant floor network, it could be vulnerable to compromise. And if compromised, an attacker could potentially gain access to production systems that keep your facility running. The device itself might be innocuous. But on a network it wasn’t supposed to be on, with systems it wasn’t supposed to access, it becomes a risk vector.
School: A school decides to refurbish its main conference room to impress visitors and parents. They install a new smart TV for presentations. Someone plugs it into the nearest network jack without thinking about which segment that jack connects to. The TV is now on the camera segment—connected to the same network as your security cameras. Nobody knows this happened. The IT team’s network diagram doesn’t reflect it. Your network inventory doesn’t track it. But now malware on that TV—whether from a compromised USB drive someone plugged in, or from a vendor update gone wrong, or from a drive-by exploit—is on your camera segment. That malware can move laterally through the segment, looking for other devices to compromise. An attacker gaining access means someone could potentially watch students, classrooms, and facilities without your knowledge. That’s not just a data breach. That’s a profound violation of student safety and trust.
Healthcare Organization: An employee wants to use a connected device in their workspace. A temporary monitoring device gets installed during an emergency. A vendor system gets connected to the clinical network for remote support and never gets removed. A contractor’s laptop stays on the network after a project completes. Each time, someone makes a reasonable decision in the moment. But over time, your clinical network accumulates devices you didn’t plan for. Some have security postures you haven’t verified. Some connect to external systems you don’t control. If an unauthorized device connects to the clinical network, it could be vulnerable to compromise. And if compromised, an attacker could potentially access patient data, modify treatment records, or disrupt clinical workflows. The impact isn’t just financial loss or reputational damage. It’s medical impact.
In every scenario, the common thread is clear: unexpected devices on your network became security risks. They introduced entry points. They introduced unknowns. They changed the actual security profile of your network without your knowledge or approval. And the longer they remain on your network undetected, the greater the opportunity for an attacker to discover them, compromise them, and use them as a foothold into your most critical systems.
Why Network Access Control Often Stays Limited
Before we talk about solutions, I want to explain why traditional network access control approaches face fundamental barriers in modern organizations. Understanding these obstacles shows why a different approach is necessary.
The Authentication Problem
802.1X requires every device to support authentication. The device must have software that can run an authentication agent and support modern cryptographic protocols. This works for corporate workstations. But many devices in modern networks fundamentally cannot participate in this model.
Consider the reality of modern network diversity: Purpose-built IoT devices—think sensors, smart cameras, and monitoring systems—were designed for a specific function with minimal computing resources. These “IoT” devices simply cannot run authentication agents. Industrial control systems—PLCs, process controllers, manufacturing equipment—are often called IIoT (Industrial IoT). These systems were designed for industrial environments and must prioritize reliability and deterministic behavior over security. They often run proprietary firmware that cannot be modified. Medical devices—monitors, ventilators, diagnostic equipment—are called MIoT (Medical IoT). These devices are regulated and certified for specific configurations. Updating them to support authentication would require regulatory recertification that could take months or years. Legacy systems that predate modern security standards simply cannot be updated. A 15-year-old manufacturing controller certified for your production process cannot be updated without risking compliance violations and operational disruption.
You can’t retrofit 802.1X onto these devices without fundamentally changing them or removing them from service. So organizations deploying 802.1X end up with limited deployments. They cover the segments where devices support authentication—corporate networks, managed endpoints, IT infrastructure. The segments that don’t—the plant floor (IIoT), medical device networks (MIoT), and sensor networks (IoT)—remain outside the access control deployment. These single-purpose devices were never designed to be authentication participants, and expecting them to be ignores how modern organizations actually operate.
The Discovery Problem
Traditional access control requires knowing upfront what devices should be on your network. But building that comprehensive inventory takes enormous effort. You need to survey every segment, identify every device, classify it, document its purpose. For organizations with thousands of devices across multiple sites, this can be a massive undertaking. And maintaining that inventory is even harder. Every time equipment changes, gets upgraded, or gets added temporarily, your inventory needs updating. In most organizations, that update process is manual and has lag. Equipment gets added and the inventory isn’t updated. Equipment gets removed and the inventory still tracks it. Over time, the inventory becomes increasingly inaccurate—which means access control based on it becomes increasingly ineffective.
The Infrastructure Barrier
Traditional NAC deployments often require infrastructure changes. You might need new switches that support the authentication protocols. You might need RADIUS servers for authentication. You might need network management systems to create policies and enforce them. For organizations with limited budgets or a multi-generation infrastructure, these upgrades are expensive and complex. A small remote office might have older switches that don’t support modern authentication. Upgrading just that site is disproportionately expensive. Or the company might manage multiple sites with different hardware vendors, making standardized deployment difficult.
So organizations make rational business decisions. They deploy access control where the infrastructure already supports it and where the device mix is homogeneous. That creates limited coverage. And your most diverse, most difficult to control network segments—the plant floor, medical devices, IoT systems, remote sites—often remain unprotected. Those segments are exactly where drift tends to accelerate most.
The Control Friction Problem
Here’s a critical insight: traditional access control assumes your network is relatively static once you’ve deployed controls. You design your policies. You implement them. Then they stay that way until the next project.
But modern networks aren’t static. They change constantly. New devices are added. Equipment is upgraded. Temporary systems are installed. Contractors need access. Business requirements shift. If your access control is static but your network is dynamic, your controls gradually become less relevant.
Here’s a specific example that shows exactly how this plays out: A hospital system acquires a smaller regional hospital to expand their network. Both organizations have some device management in place—not comprehensive, but covering key clinical segments and infrastructure. Now they face integrating two separate clinical networks with different equipment, different vendors, different architectures, and different security policies.
The challenge is immediate: the two hospitals use different monitoring equipment, different EHR integrations, and different device types on their clinical networks. The acquiring hospital’s access control was designed around their specific devices and vendor relationships. It can’t simply extend to the acquired hospital’s equipment because those devices were never on the approved list. Regulatory compliance says they can’t just merge networks without proper controls. Operations says the integration has to happen within weeks. Neither access control system can handle the complexity and diversity of equipment in the merged environment.
So they make a pragmatic decision: they create exceptions. They build workarounds. Clinical teams get manual approval processes that slow down patient care improvements. The access control that was supposed to secure both networks becomes a blocker instead. Changes require approvals. New equipment requires exceptions. Integrating new clinical solutions requires workarounds. And gradually, the workarounds become standard practice. The control system exists in name but not in practice. Both networks have evolved, but the access control approach hasn’t.
Rethinking Access Control: Continuous Visibility and Response
Here’s what I’ve learned from organizations that actually maintain effective network access control: they don’t rely on static policies set once at deployment. They rely on continuous visibility into what’s on their networks and continuous ability to respond when something changes.
The question isn’t “did we approve this device upfront?” It’s “is this device one we know belongs here right now?” The security model is based on continuous comparison to reality, not on authentication protocols or device pre-registration. This is a fundamentally different approach than traditional NAC.
Think about why this matters. Traditional NAC asks you to make all decisions upfront: which devices are approved, which users can connect, which policies apply. Once deployed, those policies stay relatively static. Changes require approval processes, policy updates, testing—all of which take time and effort. In the meantime, your network has likely changed in ways those policies don’t account for.
Continuous visibility and response inverts that model. You observe what’s on your network right now. You understand the baseline. When something deviates from that baseline, you detect it immediately. You can then make an informed decision: Is this deviation expected? Is it authorized? Is it a threat? Should I approve it, restrict it, or block it? This gives you actual control in real time, not control based on assumptions made weeks or months ago.
This works because you can see exactly what devices are on each segment at any given moment, you can establish what “normal” looks like for that segment based on actual data, when something deviates from normal you know about it immediately, and you can respond—investigate, approve, restrict, or remove the device. Your security model adapts as your network evolves. You’re not trying to predict the future. You’re responding to the present.
For access control specifically, this means you can control which devices operate normally on each segment, restrict unknown devices, and maintain your intended network boundaries—without requiring every device to support modern authentication, without needing massive infrastructure changes, and without static policies that become outdated.
Connecting This to Zero Trust
You’ve probably heard “Zero Trust” mentioned in security conversations. Zero Trust is a framework built on one principle: don’t trust any device by default. Verify every device, every request, continuously.
Network access control—knowing what devices are on each segment and controlling access—is foundational to Zero Trust. It’s your first line of verification. But here’s the problem most organizations face: network drift creates unknowns. And unknowns break Zero Trust. If you don’t know what devices are on your network, you can’t verify them. If devices drift into segments they shouldn’t be in, your Zero Trust assumptions fall apart.
Addressing network drift is actually the first practical step toward Zero Trust. It’s foundational: you know what devices are on your network, you can verify they belong there, and you can enforce that continuously. As your security architecture matures, you can layer on additional Zero Trust capabilities—identity-based controls, behavioral monitoring, microsegmentation. But it all starts with knowing and controlling what’s on your network.
How Network Lock Works
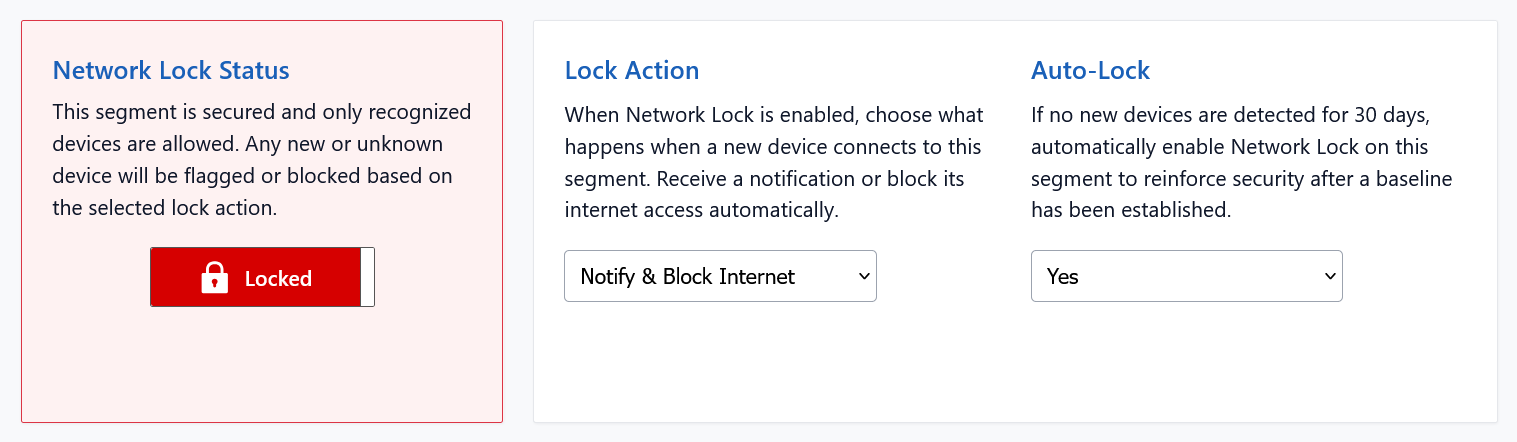
Network Lock is built on a simple model: continuous visibility into what’s on your network, combined with continuous enforcement of what should be there. This is Zero Trust in practice—trust nothing, verify everything.
Audit Mode and Block Mode work on the same dataset. The difference is the action. In Audit Mode, Network Lock sends you a notification whenever a new device connects to your segment. In Block Mode, Network Lock puts blocking rules in place for any new device that isn’t in your baseline.
That’s what makes Network Lock powerful: it can block anything without knowing it in advance. You don’t have to profile it. You don’t have to baseline it. You don’t have to pre-approve it. If it’s not on your baseline and you’re in Block Mode, it’s blocked immediately. That’s Zero Trust in action.
If this approach resonates with you, here’s the path forward. The good news: these are straightforward steps you can move through at your own pace.
- Request a Free IoT-mini™ — Go to our Next Portal, register for a free account, select IoT-mini™, and use coupon code SAVE250 for a complimentary unit.
- Activate and Discover — Connect the IoT-mini™ to your network. Within 24 hours, you will have full visibility across every segment and every device at that site.
- Enable Network Lock — Start in Audit Mode to receive notifications whenever a new device connects to your locked segment. Each notification includes a one-click link to block that device if you choose. Once you’re confident in what’s connecting, transition to Block Mode—any new device attempting to connect is automatically blocked. You still receive notifications, but no manual action is required.
- Extend to Other Networks — Repeat the process for your next critical segment.
“Network Lock has completely changed how we manage device access for our customers. The deployment is straightforward. No agents, no infrastructure overhaul, and our customers see results immediately. Within the first week, we’re discovering devices they didn’t even know were on their networks. And the blocking capability gives us real control without the typical access control complexity. It’s exactly what we’ve been looking for.”
– John Petras, CTO, Brooke Technologies
Long-Term Benefits
Over time, you move from hoping your network is secure to knowing it is. Here’s what that means:
- Complete Network Visibility: Your organization actually knows what devices are on each critical segment. Not approximately. Actually. You can answer “What’s on the plant floor network right now?” with certainty.
- Controlled Growth: When new devices are added, you know about them. They don’t silently drift into your network. They’re either approved or blocked. You maintain control.
- Faster Incident Response: When security vulnerabilities are discovered in devices on your network, you respond quickly because you know exactly which devices are affected and where. When incidents occur, you have detailed visibility into your network at that moment. What devices were on that segment? When did they connect? This accelerates investigation and response.
- Adaptive Security: Your security model adapts as your business evolves. You’re not fighting against change. You’re responding to change continuously. That’s fundamentally more resilient than static controls that gradually become outdated.
- Compliance Readiness: You have evidence of what’s on your network and proof of control. When auditors ask about device management and network integrity, you have answers backed by data.
Why I’m Writing This
After 25 years in network security, I’ve watched the industry promote increasingly complex solutions to what is fundamentally a visibility and response problem. I’ve seen organizations invest millions in infrastructure overhauls, only to find they still have drift, still have unknown devices, still have gaps in their access control.
But I’ve also watched organizations that operate differently. Organizations that accept this fundamental truth: “Our network will drift. Devices will change. Requirements will shift. That’s not something we can prevent entirely. It’s something we can detect and respond to continuously.” These organizations don’t spend years on massive projects. They don’t ask for million dollar budgets. They focus on knowing what’s on their most critical segments and maintaining control continuously.
Those organizations maintain better access control. They detect unauthorized access faster. They recover from incidents more quickly. They do all of this with fewer resources. Most importantly, they build security that’s actually sustainable—not a one time project that then becomes stale, but an ongoing practice that adapts as their business evolves.
Our team at IoT Secure built Network Lock because we kept seeing the same pattern: organizations making rational, understandable decisions—accepting partial NAC deployments, living with gaps in coverage, dealing with static controls in dynamic networks—that led to the same structural problems. IT leaders would tell us: “We know our network isn’t as secure as it should be. But traditional NAC is too complex, takes too long, costs too much. So we’re doing what we can with what we have.” And we kept thinking: there’s a better way. There has to be.
There is. It starts with understanding that access control doesn’t have to be a massive, multiyear transformation project. It starts with continuous visibility into what’s on your network and continuous enforcement of what should be there. It starts with picking one critical segment and bringing it under control, then expanding from there. It starts with accepting that your network will change, and building your security model around that reality instead of fighting against it.
Next Steps
Network drift isn’t something you can prevent entirely. But it’s something you can detect and respond to continuously. That’s the difference between hoping your network is secure and knowing it is.
The teams we work with tell us the same thing: the hardest part isn’t understanding the problem. It’s taking the first step. So here’s what we suggest: start with one segment. Any segment. Deploy Network Lock there. See what’s actually on your network. Then decide what belongs. That one decision—seeing your actual network—changes everything.
Most of our customers are surprised by what they find in that first deployment. Unexpected devices. Shadow IT. Things that have been there so long nobody remembers they exist. Once you see them, you can make real decisions: is this device supposed to be here? Should we remove it? Should we restrict it? Should we approve it? Those decisions are now based on data, not assumptions.
To get started: Book a 15-minute conversation with our team. We’ll walk through how Network Lock discovers your devices, establishes a baseline, and blocks drift. We’ll show you what discovery looks like on your type of network. Then you can decide if this is the right approach for your organization.
Book a brief demo: Use the scheduling calendar below to find a time that works.
Prefer to talk first? Call us at +1.770.224.7961 or email sales@iotsecure.io. Let’s talk about your network and what continuous access control could mean for your organization.
References
- IEEE 802.1X Overview — IEEE 802.1X (Wikipedia) — The standard protocol for port based network access control, established in 2001 to control device authentication at network entry points.
- Network Access Control — Network Access Control (Wikipedia) — Context on NAC systems, deployment approaches, and real-world implementation challenges.
- Network Segmentation — Network Segmentation (Wikipedia) — How segmentation works and why maintaining segment boundaries is fundamental to access control.
- Zero Trust Architecture — NIST SP 800-207 – Zero Trust Architecture — Authoritative framework from the National Institute of Standards and Technology on continuous verification principles.
- IoT Secure Platform — IoT Secure — Learn more about continuous visibility for network access control and device management.
- CMMC Compliance — IoT Secure for Government — How continuous access control supports compliance requirements for government contractors.